WHAT IS LET’S ENCRYPT?
Let’s Encrypt is a certificate authority (CA) run by the Internet Security Research Group (ISRG), a non-profit organisation based in California. In its own words, Let’s Encrypt is ‘a free, automated, and open certificate authority, run for the public’s benefit’.
The idea behind Let’s Encrypt is to ‘create a more secure and privacy-respecting web’. With Google nudging everyone towards HTTPS, and the major browsers moving to highlight HTTP sites as non-secure, this clearly reflects an industry-wide effort to enhance security standards across the web.
But as a small organisation relying on sponsors and donors, Let’s Encrypt has to be smart in how it delivers its services. Compared to commercial CAs, Let’s Encrypt makes extensive use of automation, with fully automated systems handling the issuing and renewal of all certificates.
While Let’s Encrypt certificates are only valid for 90 days (commercial certificates generally expire after two years), auto-renewal is available to ensure that a website isn’t temporarily left without HTTPS.
This focus on automation is a big part of how Let’s Encrypt keeps its costs down, and ultimately delivers HTTPS for free.
So with SSL certificates available for nothing, why would anyone pay for one? In terms of the actual encryption method, there’s no difference between a certificate from Let’s Encrypt and one from a commercial provider. However, there are various areas where Let’s Encrypt can’t compete with the premium CAs.
HOW IT WORKS?
The objective of Let’s Encrypt and the ACME protocol is to make it possible to set up an HTTPS server and have it automatically obtain a browser-trusted certificate, without any human intervention. This is accomplished by running a certificate management agent on the web server.
To understand how the technology works, let’s walk through the process of setting up https://example.com/ with a certificate management agent that supports Let’s Encrypt.
There are two steps to this process. First, the agent proves to the CA that the web server controls a domain. Then, the agent can request, renew, and revoke certificates for that domain.
DOMAIN VALIDATION
Let’s Encrypt identifies the server administrator by public key. The first time the agent software interacts with Let’s Encrypt, it generates a new key pair and proves to the Let’s Encrypt CA that the server controls one or more domains. This is similar to the traditional CA process of creating an account and adding domains to that account.
To kick off the process, the agent asks the Let’s Encrypt CA what it needs to do in order to prove that it controls example.com. The Let’s Encrypt CA will look at the domain name being requested and issue one or more sets of challenges. These are different ways that the agent can prove control of the domain. For example, the CA might give the agent a choice of either:
- Provisioning a DNS record under
example.com, or - Provisioning an HTTP resource under a well-known URI on
https://example.com/
Along with the challenges, the Let’s Encrypt CA also provides a nonce that the agent must sign with its private key pair to prove that it controls the key pair.
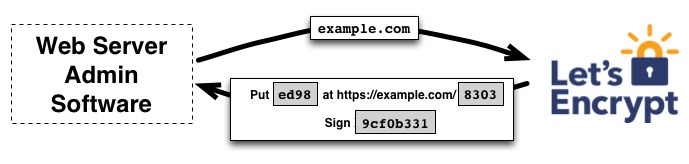
The agent software completes one of the provided sets of challenges. Let’s say it is able to accomplish the second task above: it creates a file on a specified path on the https://example.com site. The agent also signs the provided nonce with its private key. Once the agent has completed these steps, it notifies the CA that it’s ready to complete validation.
Then, it’s the CA’s job to check that the challenges have been satisfied. The CA verifies the signature on the nonce, and it attempts to download the file from the web server and make sure it has the expected content.
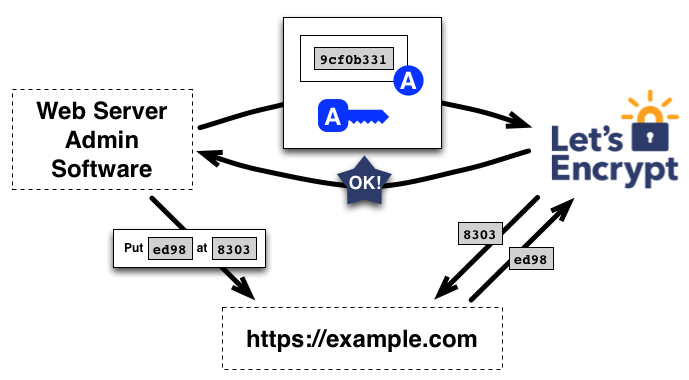
If the signature over the nonce is valid, and the challenges check out, then the agent identified by the public key is authorized to do certificate management for example.com. We call the key pair the agent used an “authorized key pair” for example.com.
CERTIFICATE ISSUANCE AND REVOCATION
Once the agent has an authorized key pair, requesting, renewing, and revoking certificates is simple—just send certificate management messages and sign them with the authorized key pair.
To obtain a certificate for the domain, the agent constructs a PKCS#10 Certificate Signing Request that asks the Let’s Encrypt CA to issue a certificate for example.com with a specified public key. As usual, the CSR includes a signature by the private key corresponding to the public key in the CSR. The agent also signs the whole CSR with the authorized key for example.com so that the Let’s Encrypt CA knows it’s authorized.
When the Let’s Encrypt CA receives the request, it verifies both signatures. If everything looks good, it issues a certificate for example.com with the public key from the CSR and returns it to the agent.
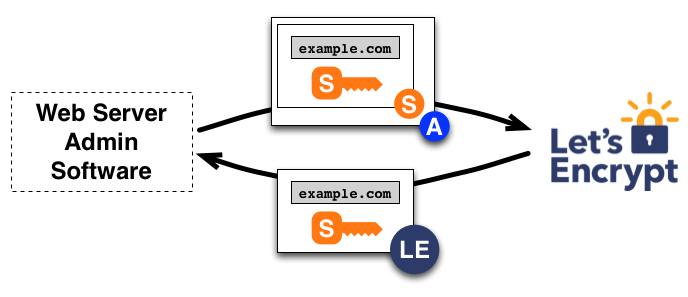
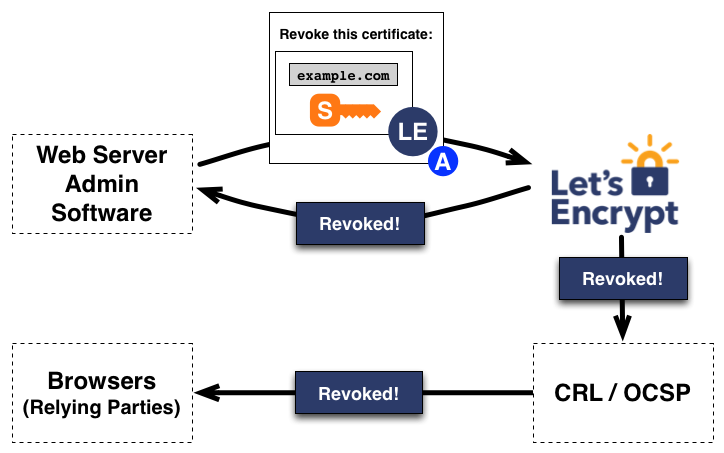
Revocation works in a similar manner. The agent signs a revocation request with the key pair authorized for example.com, and the Let’s Encrypt CA verifies that the request is authorized. If so, it publishes revocation information into the normal revocation channels (i.e. OCSP), so that relying parties such as browsers can know that they shouldn’t accept the revoked certificate.
WHY YOU SHOULD USE LET’S ENCRYPT?
- Free: Anyone who owns a domain name can use Let’s Encrypt to get a trusted certificate at zero, zilch, nada cost.
- Automatic: Software running on a webserver can interact with Let’s Encrypt to painlessly obtain a certificate, securely configure it for use, and automatically take care of renewal.
- Secure: Let’s Encrypt will advance TLS security best practices, both on the Certificate Authority (CA) side and by helping site operators properly secure their servers.
- Transparent: All certificates issued or revoked will be publicly recorded and available for anyone to inspect.
- Open: The automatic issuance and renewal protocol will be published as an open standard that others can adopt.
- Cooperative: Much like the Internet protocols themselves, Let’s Encrypt is a joint effort to benefit the community, beyond any one organization’s control.
Encryption is a vital aspect of modern communication. In short, it involves encoding data so that only its intended recipient can access it. Even if a malicious third party intercepts the message, they won’t be able to decipher its encoded contents. In addition to using encryption for sensitive information, like credit card numbers, servers use it to ensure that their communications with clients remain secure.
ASPHostPortal has a Let’s Encrypt integration, which means free SSL hosting and certificates for all of your sites. The certificate renewal process is completely automated, which in turn saves you money and time. You can literally make the switch within a click of a button. This is available from within your control panel. If you have been thinking about moving to HTTPS, now is the time.